Advanced EFS Data Recovery
Break NTFS encryption and decrypt files protected with the Encrypting File System (EFS) in Windows.
- Break NTFS encryption by attacking Encrypting File System (EFS)
- Decrypt files from users transferred to another domain, deleted accounts and disks taken offline
- Recover encrypted files if the system partition was formatted
- Search for encryption keys with low-level disk scan
- Helps analyze deleted data
Supports: all consumer and Server versions of Windows since Windows 2000 to Windows 10, NTFS, Encrypted File System (EFS), deleted users

Restore Access to EFS-Encrypted Files
Microsoft Encrypting File System (EFS) is an integral part of Microsoft Windows operating systems enabling users to protect their files against unauthorized access even from those who gain physical access to the hard disk or the computer that contains the encrypted files.
Advanced EFS Data Recovery decrypts the protected files, and works in all versions of Windows 2000, XP, 2003, Vista, Windows 7, 8, 8.1, Windows 10, Windows Server 2008, 2012, 2016. The recovery is still possible even when the system damaged, is not bootable, or when some encryption keys have been tampered with.
Advanced EFS Data Recovery recovers EFS-encrypted data that becomes inaccessible because of system administration errors such as removing users and user profiles, misconfiguring data recovery authorities, transferring users between domains, or moving hard disks to a different PC.
Usage Scenarios
Advanced EFS Data Recovery is a powerful data recovery tool that helps recovering the encrypted files under various circumstances.
- EFS-protected disk inserted into a different PC
- Deleted users or user profiles
- User transferred into a different domain without EFS consideration
- Account password reset performed by system administrator without EFS consideration
- Damaged disk, corrupted file system, unbootable operating system
- Reinstalled Windows or computer upgrades
- Formatted system partitions with encrypted files left on another disk
Recovering Encrypted Files
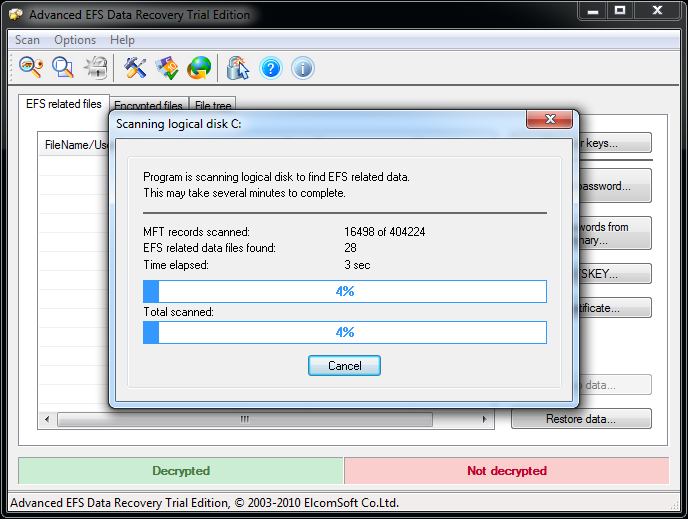
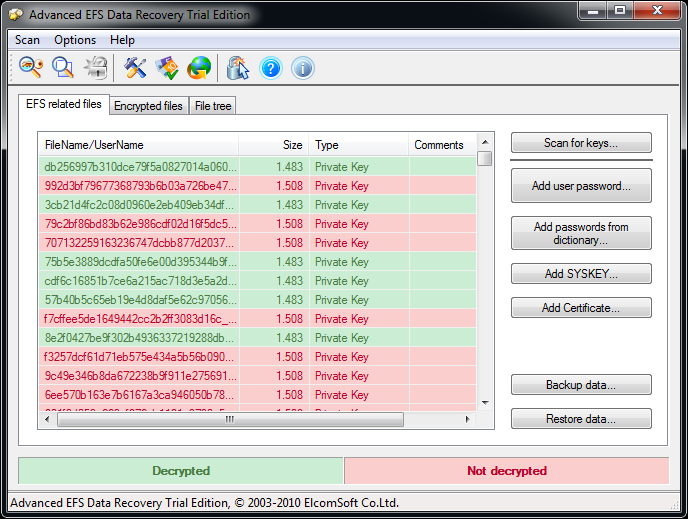
Advanced EFS Data Recovery decrypts files protected with EFS quickly and efficiently. Scanning the hard disk directly sector by sector, Advanced EFS Data Recovery locates the encrypted files as well as the available encryption keys, and decrypts the protected files. The direct access to the file system allows Advanced EFS Data Recovery to recover encrypted files in the most difficult cases even if the disk with data is only available without a valid user account to login into system, or when some encryption keys have been tampered with.
Advanced EFS Data Recovery Compatibility
–
AEFSDR Standard
AEFSDR Professional
Supports Windows
2000/XP/Vista/2003/Win7/Win8
✓
✓
Supports Windows
Server 2008/2012
✓
✓
Supports
DESX/3DE3/AES encryption
✓
✓
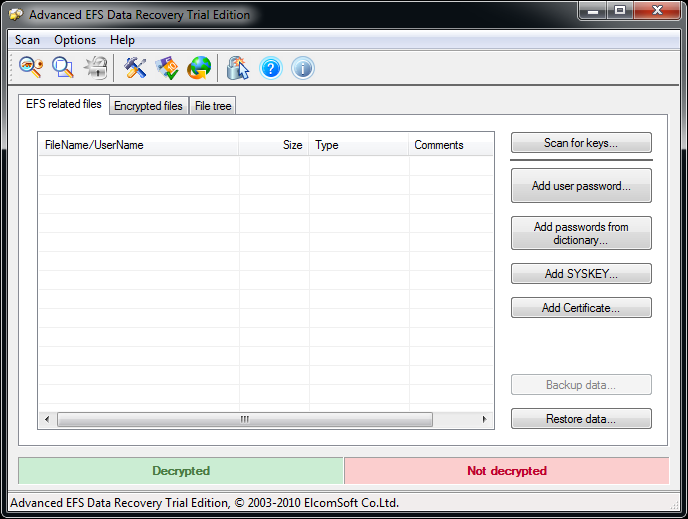
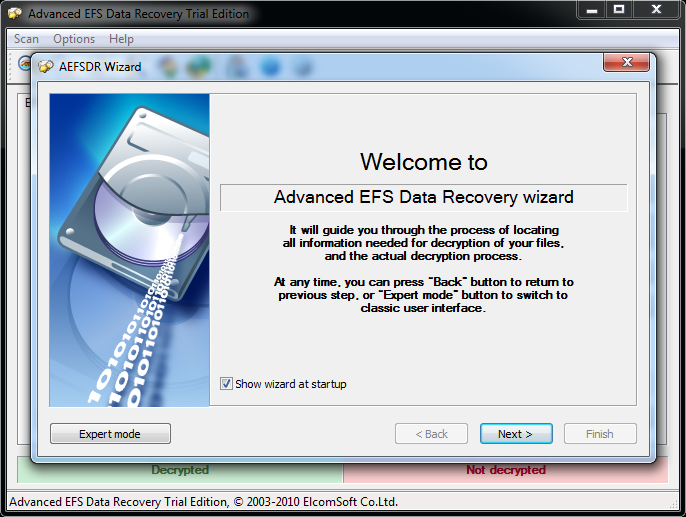
‘Wizard’ and
‘Expert’ interfaces
✓
✓
Search for
encrypted files
✓
✓
Backup/restore
keys
✓
✓
Scan for keys at
the file level
✓
✓
Scan for keys by
sectors
–
✓
Analyse deleted
files
–
✓
| – | AEFSDR Standard | AEFSDR Professional |
| Supports Windows 2000/XP/Vista/2003/Win7/Win8 | ✓ | ✓ |
| Supports Windows Server 2008/2012 | ✓ | ✓ |
| Supports DESX/3DE3/AES encryption | ✓ | ✓ |
| ‘Wizard’ and ‘Expert’ interfaces | ✓ | ✓ |
| Search for encrypted files | ✓ | ✓ |
| Backup/restore keys | ✓ | ✓ |
| Scan for keys at the file level | ✓ | ✓ |
| Scan for keys by sectors | – | ✓ |
| Analyse deleted files | – | ✓ |
System requirements
Windows
- Windows 2000
- Windows 7 (32 bit)
- Windows 7 (64 bit)
- Windows 98
- Windows Server 2003/2008
- Windows Vista (32 bit)
- Windows Vista (64 bit)
- Windows XP
- Windows 8
- Windows 8.1
- Windows Server 2012
- Administrator privileges are required
Trial limitations
An unregistered (trial) version decrypts only first 512 bytes of given files, padding the rest of content with zeros (the source/encrypted files remain untouched).
Release notes
Advanced EFS Data Recovery v.4.54.63
10 June, 2021
- support empty user password has been added
- minor bug fixes
Uninstallation procedure: in order to uninstall the product, follow the standard procedure via Control Panel – Programs and features or use the corresponding Unistall link from the product’s folder in the Windows Start menu.

Voice of Aispyer Users



More than 10 years
100% Secure & Private
24/7 customer service
0-Cost Product Update