Advanced PDF Password Recovery
Instantly unlock PDF restrictions and enable editing, printing and copying of locked PDF files. Recover original PDF passwords with configurable attacks. Break 40-bit encryption in under a minute with patented Thunder Tables technology.
- Unlock PDF restrictions (editing, printing and copying)
- Break 40-bit encryption in under a minute with Thunder Tables
- Recover original plain-text passwords with configurable attacks
- Decrypt PDF documents encrypted with 40-bit, 128-bit RC4 and 256-bit AES encryption
Supports: Adobe PDF, 40-bit and 128-bit RC4 encryption, 128-bit and 256-bit AES encryption, PDF with printing, copying and editing restrictions.

Instantly Remove PDF Restrictions
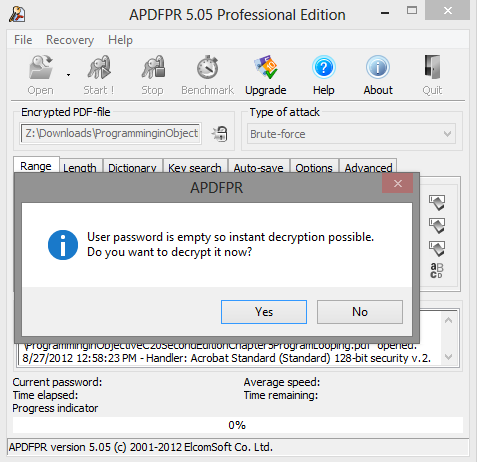
Get access to password-protected PDF files quickly and efficiently! If there is no “password to open”, or if you know it, you can instantly unlock restricted PDF documents by removing printing, editing and copying restrictions. Advanced PDF Password Recovery recovers or instantly removes passwords protecting or locking PDF documents created with all versions of Adobe Acrobat or any other PDF application.
Recover PDF Passwords
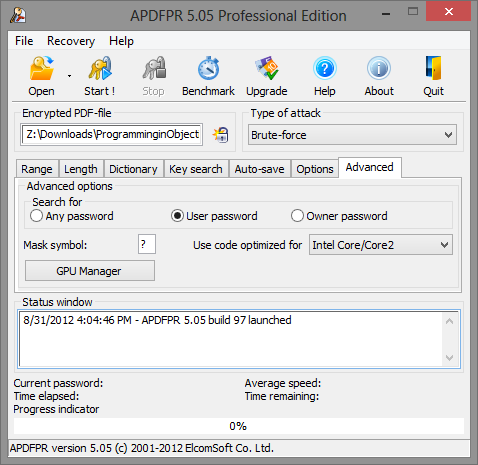
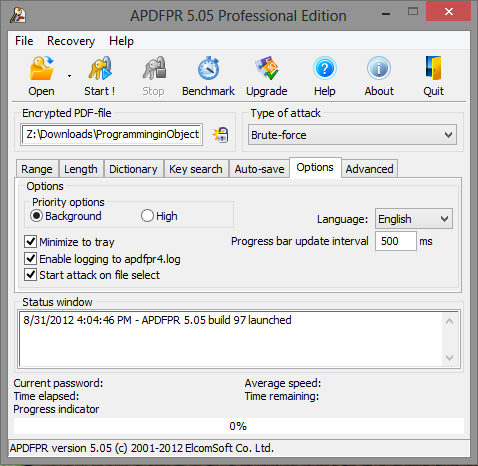
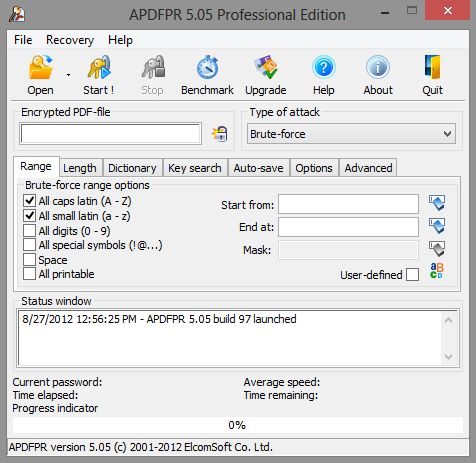
Can’t open a password-protected PDF document? You can break “password to open” by running a highly sophisticated GPU-accelerated attack. Elcomsoft Advanced PDF Password Recovery makes it easy to combine dictionary attacks with brute force. Use a combination of masks, patterns and rules to reduce the number of passwords to try. State of the art GPU acceleration enables using today’s high-performance video cards to break PDF passwords faster than ever.
Strong Password Recovery
If the PDF is protected with a strong 128-bit or 256-bit key, Advanced PDF Password Recovery performs a range of attacks on the PDF file document in order to obtain the original password. But even then you’re not left without options!
Additional Notes
DRM and Third-Party Security Plug-ins: Advanced PDF Password Recovery does not support PDF files protected using Digital Rights Management (DRM) technology or any third-party party security plug-ins such as FileOpen (FOPN_fLock).
Version 5.0 works with PDF files created in Adobe Acrobat X (with 256-bit AES encryption), with multi-core and multi-processor support and hardware acceleration using NVIDIA cards.
Advanced PDF Password Recovery Compatibility
–
APDFPR Std
APDFPR Pro
APDFPR Ent
Supports Adobe
Acrobat from 3.x to X
✓
✓
✓
Supports 40-bit
RC4 encryption
✓
✓
✓
Supports 128-bit
RC4 encryption
✓
✓
✓
Supports 128-bit
AES encryption
✓
✓
✓
Supports 256-bit
AES encryption
✓
✓
✓
Remove
restictions from protected PDF files
✓
✓
✓
Decrypt PDF files
if ‘open’ password is known
✓
✓
✓
Brute-force
attack on ‘open’ password
–
✓
✓
Dictionary attack
on ‘open’ password
–
✓
✓
Guaranteed
recovery for 40-bit encryption (takes several days)
–
✓
✓
Multi-processor,
multi-core support[1]
N/A
✓
✓
GPU acceleration
with NVIDIA cards[2]
N/A
✓
✓
Removing digital
signatures
–
✓
✓
Removing JScript
code
–
✓
✓
Removing form
fields
–
✓
✓
Guaranteed
recovery for 40-bit encryption using Thunder tables® (takes several minutes)
–
–
✓
| – | APDFPR Std | APDFPR Pro | APDFPR Ent |
| Supports Adobe Acrobat from 3.x to X | ✓ | ✓ | ✓ |
| Supports 40-bit RC4 encryption | ✓ | ✓ | ✓ |
| Supports 128-bit RC4 encryption | ✓ | ✓ | ✓ |
| Supports 128-bit AES encryption | ✓ | ✓ | ✓ |
| Supports 256-bit AES encryption | ✓ | ✓ | ✓ |
| Remove restictions from protected PDF files | ✓ | ✓ | ✓ |
| Decrypt PDF files if ‘open’ password is known | ✓ | ✓ | ✓ |
| Brute-force attack on ‘open’ password | – | ✓ | ✓ |
| Dictionary attack on ‘open’ password | – | ✓ | ✓ |
| Guaranteed recovery for 40-bit encryption (takes several days) | – | ✓ | ✓ |
| Multi-processor, multi-core support[1] | N/A | ✓ | ✓ |
| GPU acceleration with NVIDIA cards[2] | N/A | ✓ | ✓ |
| Removing digital signatures | – | ✓ | ✓ |
| Removing JScript code | – | ✓ | ✓ |
| Removing form fields | – | ✓ | ✓ |
| Guaranteed recovery for 40-bit encryption using Thunder tables® (takes several minutes) | – | – | ✓ |
System requirements
Windows
- Windows 10/8.1/8/7 (32-bit or 64-bit)
- Windows Server 2019/2016/2012
- Enterprise version only: 4 GB of free space on hard disk; USB flash drive is recommended
Trial limitations
Trial version decrypts only first 10% pages (but at least one page) of the documents, and replaces all other pages with blank (empty) ones; with a brute-force attack, passwords longer than 4 characters cannot be recovered; some dictionary-attack options are disabled; “Use pre-computed hash tables” option is not available.
Release notes
Advanced PDF Password Recovery v.5.09.163
23 July, 2021
- fixed problem with latest PDF files protected by Owner password
- fixed problem with progress bar
Uninstallation procedure: in order to uninstall the product, follow the standard procedure via Control Panel – Programs and features or use the corresponding Unistall link from the product’s folder in the Windows Start menu.

All Features and Benefits
Remove annoying restrictions from PDF files! Advanced PDF Password Recovery instantly unlocks PDF documents that restrict you of printing, editing or copying of data to clipboard. This is by far the most common protection found in PDF files. If you can open a document without a password, but cannot print it at all or are restricted to low-quality output, or if you cannot copy data to clipboard or cannot edit the document, read no further and get Advanced PDF Password Recovery Standard edition!
What if you can’t open a PDF document at all without knowing the correct password? In that case, you’ll need the password recovery feature found in the Professional and Enterprise editions of Advanced PDF Password Recovery.
The PDF format specifies two types of protection: the weak 40-bit and the strong 128-bit encryption. Advanced PDF Password Recovery guarantees the recovery of 40-bit keys by attacking the encryption key instead of attempting to guess the password. While the Professional edition takes up to several days to recover a PDF document protected with a 40-bit key, the Enterprise edition can unlock an encrypted PDF in a matter of minutes!
The unique Thunder Tables® technology developed by ElcomSoft uses pre-computed tables to significantly speed up the recovery of 40-bit keys. The technology is available in the Enterprise edition, and will unlock a protected document in a matter of minutes instead of days.
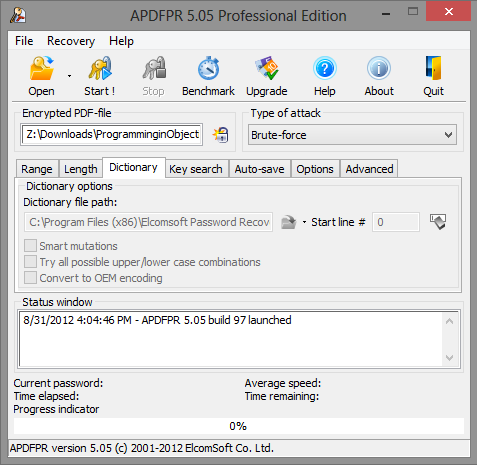
Most passwords used by living beings are based on a word or phrase. Performing a dictionary attack by attempting different combinations of cases and variations of words and characters before reverting to a comprehensive brute-force attack allows for considerate time savings shall the attack succeed.
If the password does not fall into any dictionary, Advanced PDF Password Recovery attempts all possible combinations of passwords by performing the brute force attack. The highly optimized low-level code provides the best-in-class performance for the brute-force password recovery. Multi-threaded optimization ensures optimum performance on the modern multi-core CPUs.
Voice of Aispyer Users



More than 10 years
100% Secure & Private
24/7 customer service
0-Cost Product Update